Network optimization by correcting errors that generate unnecessary Broadcast
Network optimization uses platform traffic monitoring as a way to identify performance problems and at best, to prevent these.
When we monitor a network segment we can observe both Unicast traffic and Broadcast and Multicast traffic, so in general, the number of Unicast packages is much larger, this traffic becomes a vital element of analysis.
However, we are aware that the presence of Broadcast and Multicast traffic implies a risk in the overall performance of the network, since the generation of an excessive amount of this type of packages can even lead to the total collapse of the platform.
In this article, in order for you to get to know more about Network optimization, we will draw attention to that Broadcast and Multicast traffic that, without becoming excessive, can also deteriorate the overall performance of an IPv4 platform.
We are talking about the “unnecessary” Broadcast and Multicast traffic, the one that is present in a platform due to errors in the configuration and administration of the devices that comprise it.
The effect of this traffic should not be evaluated by the total number of packages, but by the effect that these packages have and could have on the overall performance of the platform.
Let’s remember that each Broadcast package implies that all network segment switches will make a copy of that package and place it on each of its ports, and that each device must execute an input output interrupt to analyse it.
If we assume that the package is unnecessary, all the previous process will be done so that the devices finally discard the package.
Thus we arrive at our proposal, which is to establish a network optimization strategy based on:
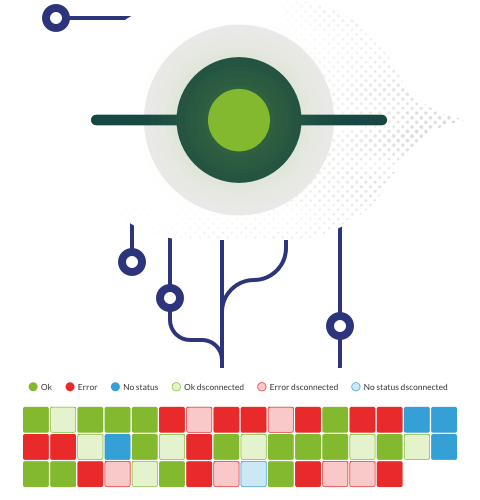
- Monitor each network segment.
- Analyse Broadcast and Multicast traffic with the premise that all this traffic must be justified.
- Identify the configuration fault that is the source of unnecessary Broadcast and Multicast traffic.
- Apply the necessary support activities with the idea of eliminating it or minimizing its effect
What should we look for? At first, we must concentrate on the Broadcast and Multicast traffic, which has to be recurrent regardless of the global volume of these packages or that random one that represents a risk to the integrity of the platform by its volume
Here is a list of some of the problems we can identify and correct when analysing unnecessary Broadcast and Multicast traffic:
Problems in the name resolution scheme
When a device must resolve the name of a resource, it relies on its DNS servers (domain name server) but, if the name is not resolved, the device can generate a recurring burst of unnecessary Broadcast traffic in the hope that the name will be recognized by another device on the network.
Because of this reason, when we do Broadcast and Multicast traffic analysis of a network segment, we will be able to identify devices that recurrently search for a resource and receive no response, and apply the technical support actions to eliminate the reference of the resource.
The typical example of this case: the workstations that are trying to resolve the name of a server that no longer exists on the network. Keep reading to find out more about Network optimization.
Errors in Plug and Play device configuration
Plug and play devices usually have a large number of protocols installed; the problem arises when these protocols are in the “active” state by default. This condition can lead to a recurring burst of Broadcast or Multicast traffic over the network segment.
The typical example is the installation of printers in IP segments. Since the printers are configured and active IPX / SPX protocol, what we will see when monitoring is a constant burst of IPX Broadcast traffic that is completely unnecessary.
Errors in station configuration
In general, network administrators handle standards that regulate how workstations need to be installed: which operating system should be used, which protocols, and which services should be configured. But if by accident or by the execution of a test some unnecessary protocol is configured, we will surely see, when monitoring an unnecessary Broadcast or Multicast traffic sequence associated with that protocol.
Unused network management tools
Many network equipment manufacturers, such as switches, routers and servers include among their arsenal of tools some product that allows the administration of such devices.
These tools can work due to the fact that each device generates a Broadcast or Multicast package so that the administration tool takes care of its presence. The point is, that if we do not have any tool that manages these types of devices we do not need the unnecessary traffic.
Problems with mac-address tables
If when analysing Broadcast and Multicast traffic we encounter Unicast traffic we may be in the presence of a Broadcast traffic stream called Unicast Flooding
Unicast Flooding traffic refers to traffic being routed between two devices that is converted to Broadcast traffic by the switches. This situation can occur for several reasons, but is usually a product of the insufficiency in size of mac-address tables that handle the volume of traffic passing through the switch.
Unicast Flooding traffic is a normal behaviour, especially when the switches are in the learning phase, but an excessive amount of this traffic can greatly harm the overall performance of the platform, especially its randomness feature.
Manufacturers like Cisco have developed procedures and commands to contain Unicast Flooding traffic. However, it may be interesting to further evaluate the correlation between the capacities of the tables and the size of the network segments in terms of amount of traffic.
In conclusion, platform optimization can and should be enriched by monitoring network segments, the analysis of unnecessary Broadcast and Multicast traffic and the execution of technical activities in order to eliminate or minimize their effect. So this is all you need to know about Network optimization.
About Pandora FMS
Pandora FMS is a flexible monitoring system, capable of monitoring devices, infrastructures, applications, services and business processes.
Would you like to know more about what Pandora FMS can offer you? Discover it by entering here: https://pandorafms.com
If you have more than 100 devices to monitor, you can contact us through the following form: https://pandorafms.com/en/contact/
Also, remember that if your monitoring needs are more limited you have at your disposal the OpenSource version of Pandora FMS. Find more information here: https://pandorafms.org