How a network operating system works and how to monitor it
In the early days of telephony, there were few people who had phone numbers in every town and city. There were just a few numbers to remember and if your brain failed, you could check with a telephone operator, women who always knew (and know) how to listen. Let’s see how a network operating system was born in the middle of the 20th century, right at the center of telephone networks.
Today, our mobile phones have replaced telephone operators, even to the smallest detail they can receive verbal orders about. In reality, the device is a simple and stupid terminal (but with higher computing power than the computers that took us to step on the moon back in 1969) but our voice ends up being executed on powerful servers… that perhaps are part of a network operating system.
X.500 Protocols
In the middle of the twentieth century, the different telephone companies had the ability to connect continents by means of satellites, apart from conventional submarine copper cables, which in turn were replaced over time by optical fiber. This created the possibility of connecting millions of people and millions of registered phone numbers. We needed to exchange information from telephone subscribers in an organized and decentralized but standardized way.
An idea arose in the International Union of Telecommunication (IUT) and they agreed on protocols (from X.500 to X.530) that evolved little by little. The project started in 1984. but it was not until 1986 that European and American standards reached a consensus. Also in that glorious year (I was finishing high school) NetWare® 2.0 came to light, which I consider to be a very famous network operating system that I worked with in the 1990s. But let’s get back to phone companies and their eagerness of sharing information.
Essentially, these protocols were well thought out and, although some did not go well, others were successful.
- DAP (Directory Access Protocol).
- DSP (Directory System Protocol).
- DISP (Directory Information Shadowing Protocol).
- DOP (Directory Operational Bindings Management Protocol).
The first of them was the source for LDAP (Lightweight Directory Access Protocol),that basically offered a flexible way to handle and work with information. In 1988, at the University of Michigan, they started the OpenLDAP project, opened and used in most GNU/Linux distributions. To delve fully into the monitoring issue, Pandora FMS has developed a plugin that allows you to search for a value (a person’s phone number, for example) on an LDAP server, or just to know whether it is up and running.
Now you may be wondering: what does all this have to do with a network operating system?
Network Operating System and Distributed Operating System
We will use the opposite-concepts learning method.
A distributed operating system operates fully and functionally, uniquely. They are a group of very well-known computers (called rather nodes) that look like a single, large operating system for users. It is closed, and although within its characteristics an increase in nodes is planned at any time, it is under very strict and complex rules. They are systems that take a long time to be developed due to the necessary classification of the hardware that will run it. I sidestep going into more detail, but more or less, it’s like a huge gigantic computer running a single distributed operating system.
A network operating system is also made up of many computers, some as servers, others as clients and even as both in some cases. The hardware is diverse and based on open and widely known standards, and it seeks sharing to take advantage of absolutely every penny invested so that each user can carry out their work quickly and efficiently.
Although this whole perspective of sharing resources was well understood -and requested- more than anything, due to the high cost of the equipment at that time (I mean the ratio of computing power and storage for each currency invested), there was a small detail: each server was the center of its own universe and network administrators had to be very aware, for example, of the change of location of a user from a certain network to another (create a new user account in the network that receives the employee and deactivate the previous account).
Let’s see if we can notice this on the phones: today you may live in Washington and tomorrow in London; phone books will automatically take care of the whole process and the work of the International Telecommunication Union will pay off!
Following the example, if I am a network administrator in Washington and I am in London, I can log in and my information can be checked across the seas. There are additional details, such as a copy of my data being stored in London and if there is any change in Washington, it is notified and the other way around. All of this is just wonderful and it is what drives me to continue working in the field of computing!
By the way, Pandora FMS, among its user authentication methods, can use LDAP with the help of OpenLDAP software. Later on, I will talk about other important technologies also used for the same purpose.
Netware® Novell® 4.x
A good example of a network operating system is proprietary Netware® Novell® software. Or rather, it was proprietary as it evolved to GNU/Linux when its sales declined. Today, I consider it to be virtually disappeared even though it uses free software.
I had to work, as I said, with said network operating system at the end of the last century, more to provide access to databases, shared printers and optical readers than anything else. Yes, you read correctly, not all computers had CD players -DVD had not been invented- and although they do not have such drives now, it is for another reason: the ubiquity of the Internet! An inherent feature of network operating systems is coexisting at layer 3, the network layer, so it had its own IPX / SPX network protocol, which we ran alongside the “new” TCP/IP. Take a guess on which one survived and which one fell into oblivion…
The success of this network software is that, although it was proprietary, it was always ready to coexist with other proprietary or open technologies: it also supported the AppleTalk® protocol, among others, and allowed the development of third-party modules (Loadable NetWare Modules® or NLM). But the icing on the cake was NetWare Directory Services®, based on (yes, you guessed it right) the X.500 protocol suite. I consider that this gave it the competitive advantage over others for around a decade, when a powerful opponent emerged from the very core of the Internet…
Microsoft Windows 2000®
After what must have been the millennium shock, they launched this truly professional version that we quickly adopted for its stability and secondly because it first introduced the famous Active Directory® based on versions 2 and 3 from LDAP.
Pandora FMS, in its Enterprise version, offers authenticating users through Active Directory, in addition to a complement to monitor many important aspects of this information store.
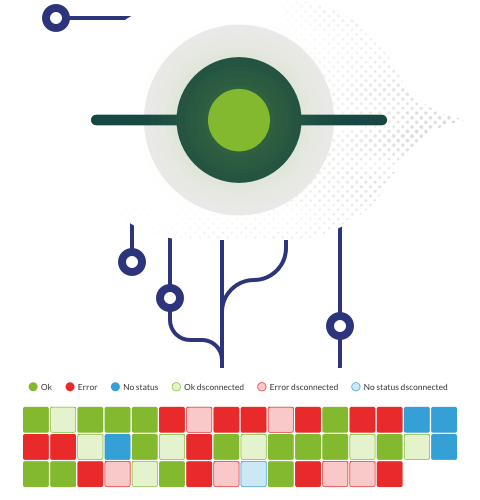
Monitoring a network operating system
I already told you how Pandora FMS has never lost sight of any technology and here I describe the features – not all though – of a network operating system, although its use has decreased considerably for its own sake, in favor of improved technologies.
- As I told you, it can be managed from any workstation, it is not necessary to be sitting right in front of the server. This may sound weird at this time, but the concept is fully current. As an example we have the Pandora FMS Enterprise Metaconsole that unites in a single console several of its different monitoring servers.
- Very efficient file server: NetWare Core Protocol® (NCP, 1983) had “embedded” commands to manage a protocol aimed at working with Network Attached Storage or simply NAS. To be honest, this has been replaced by multiple hardware expressly built for that purpose that assume the same functions of a network operating system (disk redundancy, monitoring, auditing, etc.). Pandora FMS has plugins such as Synology NAS for that popular manufacturer brand. Other important providers that Pandora FMS can monitor (right now that I’m writing): “HP Compaq Smart Array“, “Dell Server (through SNMP OpenManageServer)” and “Hitachi DF Disk Array“.
- In the previous point, with a NAS device (or several), we had our files in one (or more) very specific places, but what if we have to distribute a “disk” across a network? Look at the quotation marks: the “disk” looks like a unit, but its content is hosted on several servers… and it is as old as 1984, when it was openly developed by the company Sun Microsystems® (and later adopted by NetWare ®). If you think it is an expired technology, nothing could be further from the truth. In fact, Pandora FMS can use it if you have several Pandora FMS Dataservers, which collect and send information from software agents in a unified way (data traffic securely encapsulated through the Tentacle protocol).
- Another way to share files that has caused network operating systems to decline is the popular Samba software, based on the SMB protocol, which also allows sharing printers and, to “give it a twist”, from version 4, it supports Active Directory® as a Domain Controller. Pandora FMS has multiple plugins to monitor Samba!
Finally, remember Pandora FMS is a flexible monitoring system, capable of monitoring devices, infrastructures, applications, services and business processes.
Would you like to find out more about what Pandora FMS can offer you? Find out by going here .
If you have to monitor more than 100 devices, you can also enjoy a FREE 30-day Pandora FMS Enterprise DEMO . Get it here .
Finally, remember that if you have a reduced number of devices to monitor, you can use Pandora FMS OpenSource version. Find more information here .
Do not hesitate to send us your questions. The Pandora FMS team will be happy to help you!

Traductora a francés e inglés. Me encantan las lenguas. Amante de la ropa oversize, la tarta de queso y el chocolate caliente en invierno. Me gusta leer, escuchar música, viajar y explorar cosas nuevas. Mi frase más temida por aquellos que me conocen es “he estado pensando…”
Translator into French and English. I love languages. Lover of oversized clothes, cheesecake and hot chocolate in winter. I like reading, listening to music, travelling and exploring new things. My most feared phrase by those who know me is “I’ve been thinking…”