Certification Authority Authorization (CAA). How does it work?
The Certification Authority Authorization is an additional specification or standard that brings extra security confirmation for our web domains. In this article we will describe, in general terms, its origin, how it works and recommendations in order to implement it.
Domain Name System
In a previous article we talked about a tool to manage the assignment of private IP addresses, which is also used to manage the public IP addresses assigned to us by the authorities and/or international organizations working in this area. The truth is that memorizing those public IP addresses assigned to our web servers is definitely not fun. Actually, we, as human beings, are bad at remembering numbers, except for the balance of our bank accounts.
Therefore, it was decided to name the resources on the Internet, a Uniform Resource Locator or URL. And in order to remember the name of those resources and to associate them with the IP addresses of the computers that host them, we began to use simple text files: for each line a resource and an IP address.

In the 21st century, with the very modern advances in technology, and with the Internet of things and radio frequencies in 5G, and even with autonomous cars, in our advanced computers we access these resources through a very advanced… file. No, we are not lying to you, if you use GNU/Linux look for the file “/etc/hosts” and if you use Microsoft Windows® it is located in “c:\windows\system32\drivers\etc\hosts”. Don’t be afraid to open it, because you can only modify it with administrator rights. If you look at it you will see something like this (GNU/Linux):
127.0.0.1 localhost 127.0.1.1 KEVIN # The following lines are desirable for IPv6 capable hosts ::1 ip6-localhost ip6-loopback fe00::0 ip6-localnet ff00::0 ip6-mcastprefix ff02::1 ip6-allnodes ff02::2 ip6-allrouters
The first line indicates that every domain that has localhost is “served” by your own computer. If you want to record the fixed IP address of your web server on the Internet – that precious computer that stores your blog or personal page – by simply adding the numeric IP address to the file and then the domain on the same line, you will always have it at hand and quickly for your computer. But what about the rest of the world? How will they know? Will you have to mail this file to all your friends, colleagues and co-workers? What if the one who provides you with web hosting moves the server to a new IP address? The Domain Name Systems or DNS, as they are popularly called, come into play here.
Domain Name System, DNS
We will continue to simplify this as much as possible: your computer first searches the file and then checks with a service that remembers the domains and their IP addresses on a massive scale. Generally, whoever provides you with a connection to the network of networks has its own name resolution service, and if the address you are looking for is not stored, then it goes and asks for us to the higher authority, obtains it and keeps a copy for future reference and sends us the IP address of the resource we have requested.
The fact that each Internet provider has its own devices contributes to speeding up and decongesting traffic; even we can have our own DNS server at home or in the office, or we can choose a different one. At this point we must be especially careful with the one we choose (generally our Internet provider’s is secure enough and is established automatically when we connect), because it will lead us to the real owners of the pages, high point for banking institutions and our money (we do not want to end up in a site that hosts fake pages and steals our credentials). But it turns out that even when we connect to real websites, the sending of our credentials is also within the reach of many intermediaries who send our data packets to connect. For this reason, Security Certificates have been developed by means of powerful mathematical algorithms: to prevent attacks from intermediaries (“man-in-the-middle attack”).
Security Certificates
In Pandora FMS we are flexible and we will use any didactic resource to illustrate our advanced monitoring features. What does this have to do with security certificates?
Strict international standards were established for companies that work as Security Certificates vending machines. Essentially, we buy a file that contains a private key for which we are solely responsible and a public key that we will send to the visitors of our website so that they can encrypt everything they have to send us and so that they can decipher everything we send them.
So far so good, but this certificate must be endorsed by a valid and reliable Certification Authority, and this is taken care of by our web browser such as Chrome®, Microsoft Internet Explorer®, Edge®, Mozilla Firefox®, Mac Safari® and Opera®. We will identify if a site is secure by its https prefix and our web browser will generally indicate us with a padlock icon with some colour. Some browsers will even refuse to show us pages that do not have a secure connection protocol.

This Certificate of Security, once issued in our name, with our web domain (except the private key), becomes a completely public document worldwide and has a structure with basic data, including its expiration date. Remember how we implemented from distant times a file where we can store IP addresses and domains? So, in a similar way, our web browsers (in order to save time) come at once with the most common Security Certificates. Therefore, large corporations acquire certificates with several years of validity, in order to save billions of bytes in Internet traffic.
Usurped Identity Certificates
What would happen if a malicious person usurps, in some way, our identity and acquires a Certificate of Security with our web domain? We’ll immediately think about what that person is going to do with that, if the DNS servers are always in charge of directing any name resolution to our web server’s fixed IP address. The attacker can use the fraudulent Security Certificate in at least two possible ways:
- That person could send emails in HTML format with web addresses that mask the domain of the same attacker, thus appearing to be our website. Once there, the fake security certificate will connect securely and may mislead the visitor by impersonating us.
- Something more sophisticated could be to offer free wireless Internet in a public place and set up your own DNS server, so that the people who connect there, when entering our web domain, provide you with the IP address of the fake web page, which also has a security certificate that will complete the deception.
With this entire scheme, how could we defend ourselves?
Certification Authority Authorization
The issue of the Certification Authority Authorization is a recent issue, implemented in October 2017, but its work has been going on for years (only in November 2017 Microsoft Azure® DNS was updated to the new regulation). Even for Wikipedia®, in our own language we had to add it in order to contribute to the dissemination of knowledge.
Obtaining usurped Security Certificates from large companies such as Gmail®, Hotmail®, and Yahoo! Mail® happened for the first time in 2011 and was not an isolated event. The attackers have managed to obtain these certificates from specialized companies, such as Comodo® and DigiNotar®, and it is not yet known how much they have achieved with them. The truth of these cases is that the certificates were revoked. Revoking them implies that when a web browser goes to these certifying bodies and consults the validity, it is denied (in the same way it happens when the certificates have expired). But they ran into another problem: web browsers kept copies of them, so they compiled them, giving them precise instructions that these certificates would not be accepted if used on any web server.
To avoid future problems the technology industry turned to the Internet Engineering Task Force (IETF), to establish a new standard: the Certification Authority Authorization. Remember the DNS? Well, they are used to house a new field that we must place: the company from which we bought the security certificate. How would this work if the attacker provided a obfuscated web link in an email, is it leading the victim through DNS?
In order to complete the standard, it was established that it is the additional duty of web browsers to take the domain indicated in the certificate, to look for it in the trusted DNS, to check the Certification Authority Authorization so that this matches the one that has issued the certificate. Therefore, we explicitly declare, in the DNS, the company from which we have acquired the certificate.
Even the norm contemplates that we can include our e-mails of contact in case some irregularity is detected by some of the web browsers.
Pandora FMS, DNS and add-ons
For years, Pandora FMS has had a complement or plugin for DNS for monitoring purposes and we have published how to create a remote plugin that verifies if a security certificate has lost its validity. This is possible because of the incredible flexibility of Pandora FMS, procedures and values so that they are collected by the Data Server, through the Tentacle protocol (or are executed by the Pandora server).
We have at least two ways to obtain consulting a DNS on Certification Authority Authorization: via HTTP and command line.
Via HTTP
Google provides us with a graphical web browser interface via the address bar. In the following figure we highlight these details:

Via command line
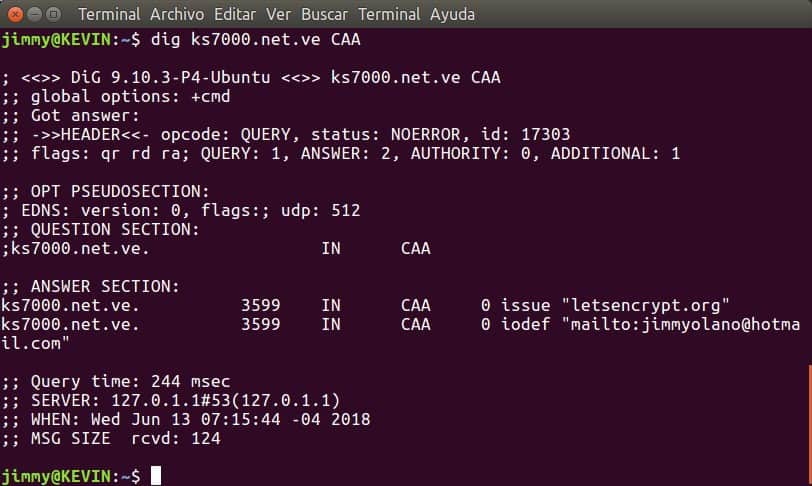
For the command line we can either use curl with the previous point, or we can use dig (Domain Information Groper), but we must have version 9.10.3 or higher registered:
Contact us
Are you interested in this plugin for your Pandora FMS Server?
Do you use Pandora FMS in your local area network?
Contact us, we will gladly help you!

Programmer since 1993 at KS7000.net.ve (since 2014 free software solutions for commercial pharmacies in Venezuela). He writes regularly for Pandora FMS and offers advice on the forum . He is also an enthusiastic contributor to Wikipedia and Wikidata. He crushes iron in gyms and when he can, he also exercises cycling. Science fiction fan. Programmer since 1993 in KS7000.net.ve (since 2014 free software solutions for commercial pharmacies in Venezuela). He writes regularly for Pandora FMS and offers advice in the forum. Also an enthusiastic contributor to Wikipedia and Wikidata. He crusher of irons in gyms and when he can he exercises in cycling as well. Science fiction fan.
















