Common vulnerabilities
and exposures
Identify, define, and catalog publicly disclosed cybersecurity vulnerabilities
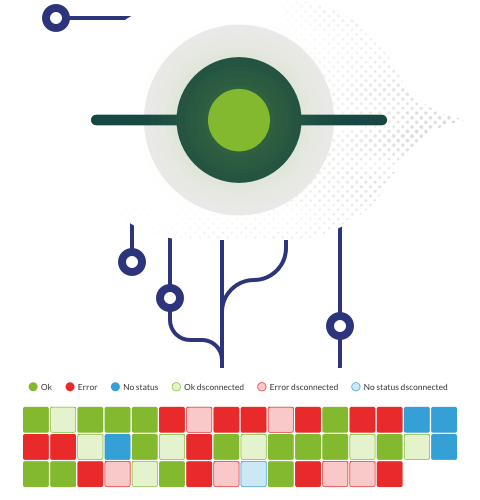
Common Vulnerabilities and Exposures (CVE®) is a list of common identifiers for publicly known cybersecurity vulnerabilities.
Use of CVE Records, which are assigned by CVE Numbering Authorities (CNAs) from around the world, ensures confidence among parties when used to discuss or share information about a unique software or firmware vulnerability, provides a baseline for tool evaluation, and enables automated data exchange.
CVE is an international cybersecurity community effort. In addition to the contributions of the CVE Numbering Authorities, CVE Board, and the CVE Sponsor, numerous organizations from around the world have included CVE IDs in their security advisories, have made their products and services compatible with CVE, and/or have adopted or promoted the use of CVE.
When a security researcher contacts us to report a vulnerability, we ask for details and try to understand the problem. If it exists, we reproduce the bug and prioritize its correction. We ask the researcher not to publish the details of the vulnerability until we have released the fix in an official version and, in coordination with the researcher, we manage the response to our customers and community.
| CVE code | Vulnerability details | Publication date | Fixed in version |
| - | No controlled file uploading | - | 96 |
| - | Users enumeration in login page | - | 96 |
| - | Credential management in process_user_login function | - | 96 |