To access the Internet, a public IP address is required, although you may also use a private IP address on your own private network. This is achieved through the translation of a private IP address to a public IP address, supported by an IP address translator or Network Address Translator (NAT).
NAT operation
Its function is to allow multiple devices (PC, tablet, laptop, cell phones, servers, etc.) to access the Internet through the same public address by translating a set of IP addresses, usually internal, to be understood by another set of addresses, usually external (Internet) and vice versa.
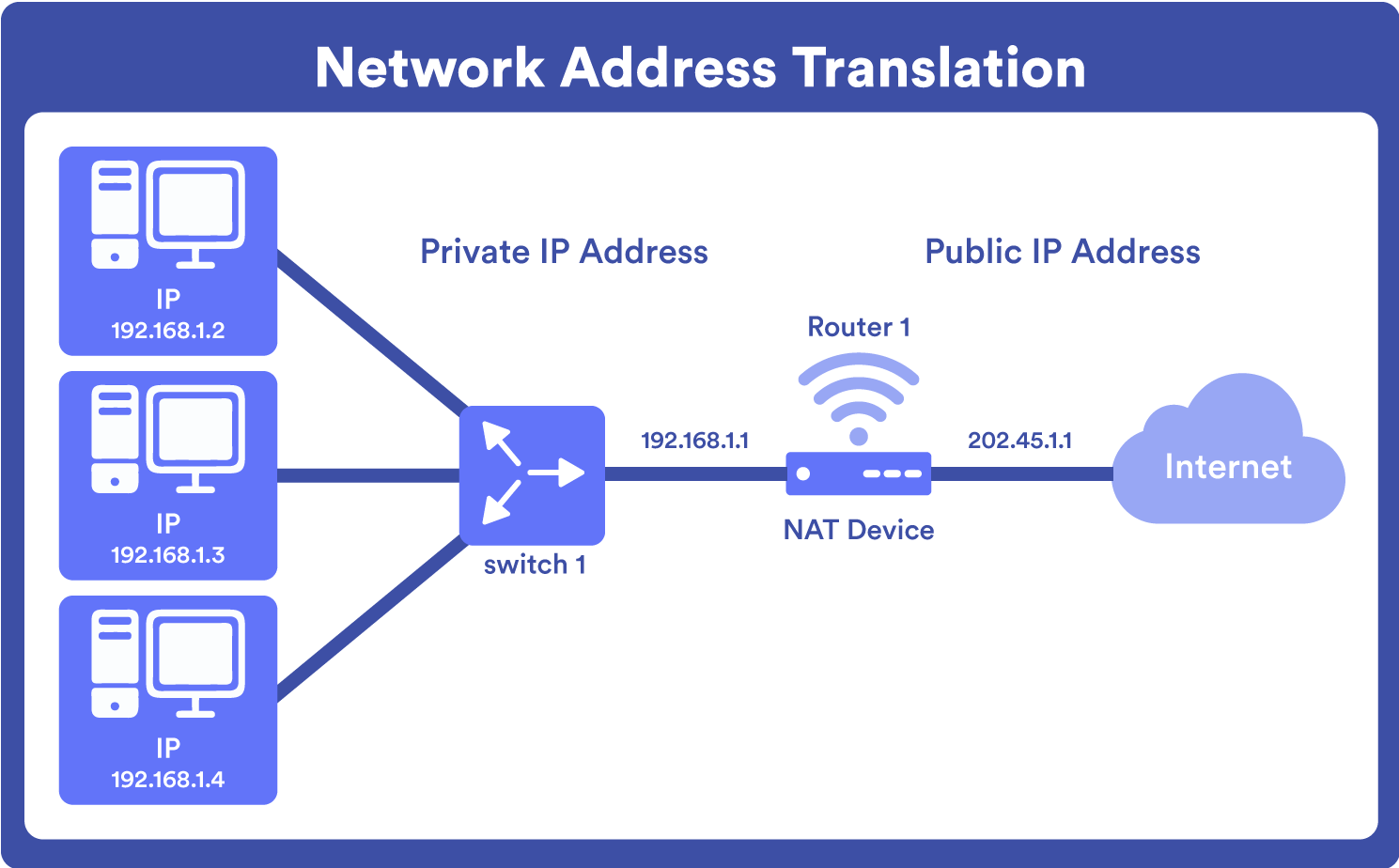
This helps a number of devices connected to a local network to be able to use the same external IP address for internet use.
As we mentioned before, using NAT one or more local IP addresses are translated into one or more global IP addresses and vice versa to give access to the Internet; but port numbers are also translated. That is, the host port number is masked with another port number in the data packet to be routed to the destination. It then makes the corresponding IP address and port number entries in the NAT table, which usually operates on a router or firewall.
To make this clearer, the edge router is typically configured for NAT, with one interface on the local (internal) network and one on the global (external) network. When a packet traverses outside the local (internal) network, NAT converts that local (private) IP address into a global (public) IP address. When a packet enters the local network, the global (public) IP address becomes a local (private) IP address.
Once this is understood, we must talk about masking: suppose that in a network there are two hosts (A and B) connected and both request the same destination, on the same port number (say 1000), on the host side, at the same time. If NAT only translates IP addresses, when the packets arrive at NAT, both IP addresses will be masked by the public IP address of the network and sent to the destination. The destination will send responses to the router’s public IP address. Therefore, upon receiving a response, NAT will not make clear which response belongs to which host (because the source port numbers for A and B are the same). Therefore, to avoid this problem, NAT also masks the source port number and makes an entry in the NAT table.

With this, we see that NAT performs two basic functions: assigning one or multiple public IP addresses for the local network and simplifying addressing by masking private IP addresses.
Types of NAT
Due to its configuration, there are three different types of NAT with different functions:
1. Static NAT where a fixed and permanent association is established between a private IP address on the local network and a specific public IP address. It is generally used for web hosting, not for organizations where there are multiple devices because each device would demand a public address, which would be very expensive and difficult to manage.
2. Dynamic NAT where a set of available public IP addresses is set for a device on the local network to request access to the Internet and be temporarily assigned an available public IP address by the local network. In case the IP address of the group is not free, the packet will be discarded, as only a fixed number of private IP addresses can be translated to public addresses. Understanding this, this type of NAT can also be very expensive as the organization has to purchase many global IP addresses to create a pool.
3. NAT PAT (Port Address Translation) where an association is established between local network devices and a single public IP, differentiating in each device a port that is assigned to receive the corresponding network traffic for each device. PAT seeks to retain the initial source port. In case the initial source port is already in use, the next available port is assigned, in an ongoing process, until no more external IP addresses or ports are available.

This type of NAT is most often used because it is the most cost-effective, as thousands of users can connect to the internet using only a real global (public) IP address.
NAT security
Today, many network engineers turn to using NAT to protect their devices on the network from cyberattacks, as it acts as an extra layer of security between devices on a private network and the internet. This is because the NAT router or NAT firewall can sort and verify data as it is sent to a device, hiding internal IP addresses, leaving them inaccessible from the internet. This can help prevent attacks such as port scans, which allow vulnerabilities to be identified in devices on the network.
NAT also allows integration with firewalls of routers and network devices, improving security policy implementation.
Another important aspect of security is that NAT helps prevent private IP exhaustion, as using a single public IP address for multiple devices on a network also helps ensure that the allocation of public IPs is as efficient as possible.
It is worth mentioning that private addresses cannot guarantee full security. Of course, you should also use encryption and other security tools. You should also keep your devices on a local IP address as a good extra security measure.
Advantages and disadvantages of NAT
Among the advantages of NATs there are the following:
- NAT provides a layer of security in the network, since private networks do not advertise their addresses or their internal topology, so they are safe by controlling external access, although it does not replace firewalls.
- It increases flexibility of connections to the public network, as well as support for Internet Protocol Version 4 (IPv4). Backup/load balancing sets and sets can be implemented to ensure reliable public network connections.
- In the event of an overload, internal hosts can share a single public IPv4 address for all external communications. Very few external addresses are required to support multiple internal hosts, which also means less management and costs.
- Consistency with internal network addressing schemes. If you want to change the public IPv4 address scheme on a network without private IPv4 addresses or NAT, you must redirect all hosts on the existing network. NAT allows you to keep your IPv4 addresses private, while speeding up the switch to a new public addressing scheme.
The other side of the coin is the disadvantages based on the fact that hosts on the Internet communicate with the device with NAT and not with the real host, which implies:
- Increased delay or latency in network communication, as the translation of each IPv4 address in the data packet headers takes time.
- Possible impairment in end-to-end feature. Many Internet protocols and applications rely on addressing, from source to destination. For example, some security (digital signature) applications fail because the source IPv4 address changed before reaching its destination.
- Loss of IPv4 traceability when tracking packets in the network. This is because packets go through several address changes at different NAT hops, making them difficult to track. This impacts problem solving.
- Increased complexity in configuration and maintenance, mainly when establishing IP address and port translation rules for specific applications. For example, NAT modifies values in headers that interfere with integrity checks performed by IPsec and other protocols from tunneling.
- Possible interruptions in Transmission Control Protocol (TCP) connections. Services that require a TCP connection from an external network or stateless “protocols” may be interrupted. Unless the NAT router is configured to support these protocols, incoming packets might not reach their destination.
Performance impact
NAT helps reduce the load on the network when it allows multiple devices to share a single public IP address. This can be useful when you have few or only one Public IP available, also providing a layer of security by preventing non-identification and direct access to internal network devices.
However, it can also lead to bandwidth limitations and potential connectivity issues in network environments with a large number of devices and heavy network traffic. In NAT PAT environments, congestion may take place if there are many simultaneous connections from multiple devices, which may add additional latency in network communication and negatively affect user experience.
Carrier Grade NAT (CG-NAT)
Carrier Grade NAT (CG-NAT), also known as Large-Scale NAT (LSN), is a large-scale NAT implementation normally used by Internet Service Providers (ISPs) to manage and attempt to maintain public IPv4 addresses on their networks.
Its main function is to provide Internet connectivity to multiple clients using a single public IP address range (e.g. 100.64.0.0/10) through centralized management, performing large-scale address translation. This results in a temporary solution to mitigate the shortage of public IPv4 addresses until the full implementation of the IPv4 upgrade is completed in IPv6— bearing in mind that IPv4 enables 4,294,967,296 different device addresses, which is a smaller number than the world’s population, and, therefore, lower than the volume of devices in total.

Among the considerations to take into account, CG-NAT does not solve the problem of IPv4 address exhaustion when a public IP address is needed, such as in web hosting. You may also create a performance bottleneck that limits your scalability.
Use check of CG-NAT
To check if CG-NAT is being used in a network, it is necessary to access the router provided by the Internet service provider (ISP) and verify in its configuration if options or configurations related to CG-NAT are found within the NAT section. This can be seen in the NAT configuration options themselves as in a different section, referred to as “Carrier Grade NAT” or “CG-NAT”, where you may check its status and configuration.
In Windows operating systems, you may check if you belong to a CG-NAT by running the tracert command and pointing to your public IP. If the result is a single hop (or jump), it means that you do not belong to a CG-NAT, if the result is 2 or more hops then you do belong to a CG-NAT:

On Linux operating systems, the same procedure can be performed with the traceroute command.

Impact of CG-NAT on users
CG-NAT can have different impacts, depending on the type of user controlling the network.
- In advanced users, CG-NAT can bring complications when deploying port forwarding configurations, IPv6 tunnels, or complex remote access applications.
- In standard users, the problem may take place primarily in the remote work mode, where they may be affected when making VPN connections to the enterprise, certain video conferencing applications, and some remote access applications that rely on incoming connections from the Internet.
- In recreational users, for example in a video game, direct connections between players are required, or they rely on port forwarding for optimal performance. CG-NAT may also cause latency issues in these cases, with a direct impact on the user experience.
NAT in video games
NAT can significantly impact the online gaming experience if the user does not have the knowledge to properly configure this network mechanism. Many online video games use peer-to-peer connections between players to make real-time interaction ; So if NAT is not properly configured, users can be affected, with connectivity issues, latencies, and a less fluid or interrupted gaming experience.
For these cases, there are several solutions to improve NAT classification and optimize the gaming experience. On PC, port forwarding must be configured on the router, which may help open specific ports used by the game. This makes direct connection between players easier, reducing connectivity issues and improving NAT ranking.
On consoles, using the UPnP protocol (Universal Plug and Play) may help automatically open and redirect ports needed for better connectivity.
In other cases, upgrading the router’s firmware or even acquiring a more modern and compatible router may solve NAT issues and improve the gaming experience.
Conclusion
In conclusion, NAT plays an important role in the current connectivity of computer networks, especially in IPv4 environments, where public IP addresses are limited. It is clear that security strategists must also take into account their considerations and possible disadvantages in terms of latency and traceability. In that sense, the correct protocols and port configuration and maintenance is required to make public IP available for service use and delivery, while saving money and adding an additional security layer, which also strengthens security policies by integrating router and device firewalls.
Can one tool have global visibility?




