Secciones
- What is remote access?
- Benefits of Remote Access
- Remote access-based strategies to improve business competitiveness
- Using Remote Access in Technical Support
- Remote Access Methods
- Remote Access Operation
- Remote Desktops
- Remote Access Types
- What are remote access protocols?
- Challenges and security in remote access
- Conclusion
Of course, the most productive application of remote access takes place in the business environment. Thanks to digital transformation, improvements in connectivity and cloud storage, the number of companies using remote connections has grown. However, many still wonder: What is remote access? What are its benefits, and how to implement it safely? In this article we will try to answer these questions.
What is remote access?
Remote access is a technology that allows users to access applications and resources that are located outside the local network. This is achieved by using a combination of software, hardware, and network configurations that work together by transmitting data from one device to another over encrypted channels.
During the COVID-19 pandemic, the need to establish remote connections became a priority for companies. In the first weeks of March 2020 alone, the use of remote access tools increased by 41%. However, even before the Internet was widely available to the general public, methods for connecting computers and sharing information remotely already existed. Users connected via phone lines using modems to establish a remote connection to the central system. Then, thanks to a terminal emulation software they could interact with the system files and resources.
This type of access made it possible for companies with different branches and subsidiaries to manage their assets centrally.
With the improvement of connection efficiency and speed, remote access solutions became popular also reaching SMEs. Thanks to this technology, employees and business managers can check corporate mail from any location, create dynamic workspaces or access key data in real time to make informed decisions.
Benefits of Remote Access
Remote access solutions help improve the productivity of companies, regardless of their size or sector. Below, we’ll list some of its most prominent benefits.
Make the transition to telecommuting or hybrid work easier
For many companies, teleworking is the new norm. Thanks to remote access tools, there is now the possibility to simultaneously manage work from home and from the office.
This work flexibility increases employee satisfaction and productivity. Research by American Express found that remote workers were 43% more productive than their office counterparts.
Commuting is often a stressful experience for employees, especially in busy cities. By allowing them to work remotely, they can enjoy a less stressful workday, reducing tardiness and absenteeism.
Provide secure access to data
Enabling remote access software ensures that corporate resources will always be available. Employees can access company files from any device, share their meeting screen, and actively collaborate on troubleshooting.
Minimize operating costs
They reduce spending on office rentals and supplies. In addition, they support the BYOD policies (use of personal devices to access the corporate network), which translates into hardware savings.
Help maintain service level agreements (SLAs)
Remote management tools enable IT teams to provide quick responses to critical issues so they can meet deadlines set in SLAs.
Ensure business continuity
Transport strikes, adverse weather conditions, temporary office closures due to renovations… Situations often arise that impede travel to the office. In these cases, remote access technology plays a crucial role, ensuring business continuity and giving companies the flexibility to adapt to unforeseen circumstances.
Reduce carbon footprint
Finally, remote access also has a positive impact in terms of environmental sustainability. Fewer vehicles on the road and lower energy consumption in offices means a decrease in CO2 emissions.
Remote access-based strategies to improve business competitiveness
Remote access solutions are very versatile and can boost the competitiveness of companies in different ways:
- Knowledge Sharing: Remote access facilitates cross-team communication and knowledge sharing. It is even possible to organize remote training sessions for those employees who work outside the office.
- Incorporate the best talent: Companies are no longer obliged to limit the search for personnel to a specific area. Now, HR professionals will look for the most suitable people for the position regardless of where they are located.
- Boost sales and customer support: Sales and marketing teams can leverage this technology to make presentations and product demonstrations. In addition, they will be able to offer their customers agile support, responding to their queries quickly.
It is important to invest in strategies aligned with business objectives to optimize remote connection performance.
Using Remote Access in Technical Support
Remote access solutions are indispensable for companies offering technical support services as they allow IT teams to perform repairs and maintenance tasks from any location.
They can be used by both internal staff and external suppliers or MSP. If implemented correctly, they will improve security by monitoring network activity and detecting threats early.
Once a support ticket is generated, IT technicians can access their customer’s computer using dedicated remote access software and solve the issue within minutes without the person having to leave their desk.
Main advantages of remote management in technical support:
- It reduces expenses related to on-site management.
- It improves response times without sacrificing service quality.
- It monitors in real time the performance of servers and IoT devices connected to the network and sends alerts should it detect any suspicious activities.
- Facilitates preventive maintenance by applying massive firmware and software updates.
- For MSP providers, remote access tools allow them to troubleshoot multiple customers at once from a single central dashboard. This practice increases productivity by reducing commuting time and facilitating efficient management of multiple services.
To finish this section, we think it is important to make a distinction between assisted and unattended support.
- Assisted support (also called on-demand support) responds to a support request and requires the presence of a user at the other end of the network, who allows technicians to access their device.
- Instead, unattended support works thanks to an agent installed on the workstations. IT technicians can access it at any time without requiring access permissions. It is widely used to launch upgrades or perform maintenance tasks.
Remote Access Methods
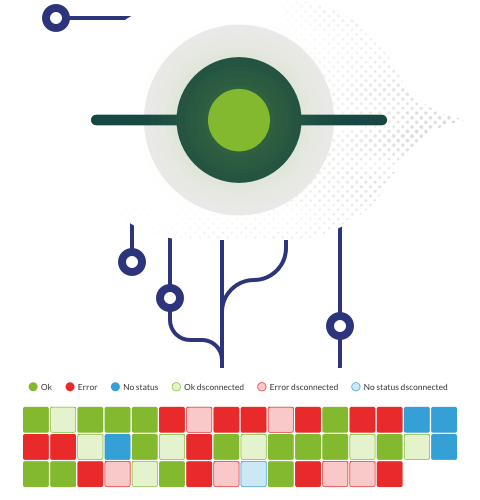
To configure a remote connection we need a safe network that allows information transmission between a local and a remote device, hardware that ensures compatibility and performance, and software that provides the necessary graphical interface.
Now, the way to create this connection can be more or less complex. We distinguish between:
- Direct Remote Access: One device connects to another directly over the network, with no other infrastructure.
- Indirect remote access: It involves the use of a server that works as an intermediary.
- VPN (Virtual Private Network): It creates an encrypted connection over a public network such as the Internet, opening tunnels through which data is securely sent. Although the first VPNs emerged in 1990 among large telecommunications companies, today they are present in almost all sectors and have become the main method of remote access due to their scalability and the security they offer.
Remote Access Operation
Remote access is based on a client-server model. The computer we want to access would be the server and the devices on the network that connect to it are its clients. Information is transferred through input and output ports using a series of security protocols such as SSL/TLS for web connections or IPsec for VPN connections.
Also, depending on the resources used during the connection, the access control will be different. We have seen that VPN provides an additional layer of security for data transmission, and also that it allows computers to be accessed remotely, but not controlled remotely. If you want to run scripts, install patches or updates, use Remote Desktop Protocol (RDP) through VPN.
RDP makes the work of IT administrators easier by providing them with a graphical interface instead of using the command line interface and can also be used in cloud environments.
Another alternative is to use SSH (Secure Shell), a cryptographic protocol to securely access and manage remote devices and systems. To open an SSH communication channel, it uses a client-side component that is a program or application to connect to another machine. The client uses the remote host information and provides identification data such as username, password and SSH keys. If the credentials provided are correct, SSH will create an encrypted communication session.
Remote Desktops
Remote desktops are programs that allow you to connect to a server or device and access the necessary resources through a web browser.
Thanks to remote desktops, IT professionals can run applications or transfer files using a graphical interface that makes it easy to manage multiple devices.
Normally, remote desktop connection is based on the Microsoft RDP protocol, already pre-installed on most Windows computers, although it is also available for Mac OS and Linux systems.
RDP opens a network channel and sends data back and forth using TCP/IP network protocols.
When setting up a remote desktop connection, it is essential to reinforce security measures with encryption and multi-factor authentication techniques. A study entitled “RDP Exposed – The Threat that’s already at your door” analyzed the attacks suffered by ten Internet-connected honeypots for a month. In this period, 4.3 million fraudulent logins were registered, both to unprivileged users and administrators.
Most cyberattacks rely on brute force (testing multiple login credentials) and exploit vulnerabilities in outdated or weakly passworded systems. There are programs that were created only to scan the Internet for open RDP ports, so it is always important to increase the security of terminals and devices with remote access.
Basic measures to strengthen the security of RDP remote connections:
- Change the default RDP port 3389.
- Use long, strong passwords based on a combination of alphanumeric characters.
- Replace the username “administrator” with a more difficult one.
- Use Remote Desktop Programs over an Encrypted VPN Connection to Increase Security.
- Implement a multi-factor authentication system.
- Restrict login attempts to 3 or 5 and lock accounts after multiple failed login attempts.
- Do not leave RDP ports open if not in use.
- Keep the software updated to the latest versions with their corresponding security patches.
- Use network-level authentication (NLA) to verify user identity before remote connection is established.
- Restrict the number of IPs so that only people in the company can connect.
If the number of devices connected to the network is important, it is best to use a total remote control software such as Pandora RC since it allows real-time monitoring of all computers connected to the network, configure alerts and see who is accessing the system at all times. It also generates reports on failed session attempts to neutralize threats before they become critical failures.
Remote Access Types
In the past, remote connections employed analog modems that connected users through phone lines to office servers and equipment. However, thanks to technological advances and the emergence of broadband , today’s businesses can enjoy faster and more stable connections.
Taking into account the infrastructure used, broadband connections can be:
- Wired: IT professionals use a Wi-Fi connection or Ethernet cables to access remote resources.
- DSL (Digital Subscriber Line): It uses conventional phone lines and offers asymmetric speeds, being faster in downloading than in loading.
- Internet Via Satellite: It is used in areas where no terrestrial connections are available.
- Mobile Internet: It provides wireless connectivity through technologies such as 4G or 5G.
- Optical fiber: It is ideal for transferring large amounts of data quickly.
What are remote access protocols?
A common concern of MSPs and internal IT teams is maintaining connection security when employees work remotely. To achieve this, security protocols are used to ensure that all data transferred during the session is converted into a code that cannot be decrypted without the correct key. That way, even if they are intercepted, they cannot be used maliciously.
The main ones are:
- PPP (Point-to-Point Protocol): It is a TCP/IP protocol that allows computer systems to be connected thanks to the Internet or a phone network. It connects two routers directly without using a host or any other network protocol. It can authenticate looped connections, encrypt transmissions, and compress data.
- IPsec (Internet Protocol Security): It creates encrypted connections between devices ensuring the security of data transmitted over public networks. It is one of the most widely used security protocols in VPNs.
- PPT (Point-to-Point Tunneling Protocol): It was one of the first protocols developed for VPN, and although it is easy to configure, it is considered less secure than other recent protocols.
- L2TP (Layer Two Tunneling Protocol): It is based on an intra-tunnel encryption protocol for data traffic. It offers greater security than PPTP.
- RADIUS (Remote Authentication Telephone Access User Service): It provides authentication, authorization, and accounting (AAA) services for remote access on a distributed phone network.
- TACACS+ (Terminal Access Controller Access Control System): It is an authentication protocol that is mainly used in UNIX networks. It differs from RADIUS in handling authentication and authorization separately, offering more precise control.
Challenges and security in remote access
When a remote access solution is enabled there is always a risk of malicious attack: phishing campaigns, theft of company credentials or sensitive data. To avoid leaks and service interruptions that may put business continuity at risk, it is important to be cautious.
Most cyberattacks are due to human error, that is, users who create weak passwords or use the default ports. Companies working with fully or partially remote teams are often challenged to change their work culture and educate employees on cybersecurity.
However, remote connections can also be protected with a system of multi-factor authentication (MFA) and Zero Trust Access (ZTNA).
MFA adds a security layer during the login process, requesting a first validation by username and password and a second validation by a unique text message (SMS) code. More advanced systems may include fingerprint checking, biometric data, or facial recognition.
ZTNA also uses the multi-factor authentication system, but further extends security by verifying each access attempt individually. This approach is based on the premise of not giving trust to users automatically, even if they are within the company’s corporate network.
Conclusion
Today more than ever, large and small companies are thinking about adopting remote access solutions to be more competitive.
We have a whole set of security measures aimed at protecting remote connections; from basic data encryption protocols, virtual private networks or authentication systems to prevent unauthorized access.
Each organization has unique security requirements, so it is recommended that the measures taken be scalable. In addition, companies with remote workers or using multiple devices should implement monitoring software such as Pandora FMS to monitor network activity and the performance of their equipment.
We hope you found this guide helpful. Remember that you can use the web browser to find other content on the blog on more specific topics.
Take control of your equipment remotely. Fast, easy and with no need to memorize or install anything